Pues, he decidido aprender más de cloud porque siento que todos mis pentests me llevan a eso. El plan general es Azure fundamentals y luego security 500 (tal vez administrator) y luego AWS Fundamentals y Security Speciality. Planeo ponerle un poco de pentesting en medio con http://flaws.cloud/ y http://flaws2.cloud para hacerlo más divertido. Después de esos tal vez CCSK o SANS.
Azure Fundamentals
Entonces en teoría la preparación del examen dura aprox 9 horas. El plan es hacerlo en dos días y el examen el día dos en la noche.
1 Cloud Concepts – Principles of cloud computing
What is cloud computing?
El provedor de cloud es responsable del hardware. Lo que normalmente te rentan es:
- Computer power (ram o procesadores)
- Storage
- Networking
- Analytics
The goal of cloud computing is to make running a business easier and more efficient. Every business has different needs and requirements. Cloud computing is flexible and cost-efficient, which can be beneficial to every business.
Benefits of cloud computing
- Cost effective (Pay as you go y sin inversión inicial)
- Escalable (vertical UP (+ cpu o ram) u horizontal OUT con más servidores).
- Elastic (puede escalar automático o manual)
- Current (ellos se encargan de mantener el hardware corriendo)
- Reliable (ellos se encargan del fault tolerance)
- Global (obviamente solo los grandes)
- Secure (de acuerdo a ellos es más seguro y tienen razón al menos en lo físico)
Compliance terms and requirements
- Criminal Justice Information Services (CJIS) para contactos con el FBI dicen que azure es el único que lo tiene
- Cloud Security Alliance (CSA) STAR Certification. ISO 27001
- General Data Protection Regulation (GDPR)
- EU Model Clauses
- Health Insurance Portability and Accountability Act (HIPAA)
- International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC) 27018
- Multi-Tier Cloud Security (MTCS) Singapore
- Service Organization Controls (SOC) 1, 2, and 3
- National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF)
- UK Government G-Cloud
Economies of scale
Que tienen economía de escala y tu no. ja
Capital expenditure (CapEx) versus operational expenditure (OpEx)
- Capital Expenditure (CapEx): CapEx is the spending of money on physical infrastructure up front, and then deducting that expense from your tax bill over time.
- Operational Expenditure (OpEx): OpEx is spending money on services or products now and being billed for them now. You can deduct this expense from your tax bill in the same year.
Cloud deployment models
- Publica (todo en azure)
- Privada (todo on-premise)
- Hibrida (combinando lo de arriba)
Types of cloud services

Understand Geographies in Azure
An Azure geography is a discrete market typically containing two or more regions that preserve data residency and compliance boundaries. This division has several benefits.
Availability Zones are physically separate datacenters within an Azure region.Are primarily for VMs, managed disks, load balancers, and SQL databases. Azure services that support Availability Zones fall into two categories:
Zonal services – you pin the resource to a specific zone (for example, virtual machines, managed disks, IP addresses)
Zone-redundant services – platform replicates automatically across zones (for example, zone-redundant storage, SQL Database).
Understand Service-Level Agreements for Azure
There are three key characteristics of SLAs for Azure products and services:
- Performance Targets
- Uptime and Connectivity Guarantees
- Service credits
Resiliency is the ability of a system to recover from failures and continue to function.
Failure Mode Analysis (FMA). The goal of an FMA is to identify possible points of failure and to define how the application will respond to those failures.
Azure management options
- Azure portal (GUI)
- Azure PowerShell
- Azure Command-Line Interface (CLI)
- Azure Cloud Shell
- Azure mobile app
Azure compute
- Virtual machines are software emulations of physical computers
- Containers virtualization environment for running applications without OS just libraries and components
- Azure App Service Azure is a platform-as-a-service (PaaS) offering in Azure that is designed to host enterprise-grade web-oriented applications.
- Serverless computing is a cloud-hosted execution environment that runs your code but completely abstracts the underlying hosting environment. You create an instance of the service, and you add your code; no infrastructure configuration or maintenance is required.
VMs
- Availability sets
- Virtual Machine Scale Sets
- Azure Batch
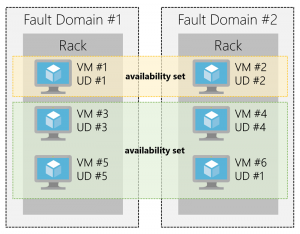
An availability set is a logical grouping of two or more VMs that help keep your application available during planned or unplanned maintenance. Your VMs are then sequentially placed across the fault and update domains. The following diagram shows an example where you have six VMs in two availability sets distributed across the two fault domains and five update domains.
Azure Virtual Machine Scale Sets let you create and manage a group of identical, load balanced VMs. The number of VM instances can automatically increase or decrease in response to demand or a defined schedule.
Azure Batch enables large-scale job scheduling and compute management. It will turn on machines, run jobs and stop machines.
Containers
Container management can be done
- Azure Container Instances (ACI) It is a PaaS offering that allows you to upload your containers and execute them directly with automatic elastic scale.
- Azure Kubernetes Service (AKS) is a complete orchestration service for containers with distributed architectures with multiple containers.
Containers are often used to create solutions using a microservice architecture. This architecture is where you break solutions into smaller, independent pieces.
Serverless computing
- Abstraction of servers: you simply deploy your code, which then runs with high availability.
- Event-driven scale: Triggers define how a function is invoked and bindings provide a declarative way to connect to services from within the code.
- Micro-billing: if the code runs once a day for two minutes, they’re charged for one execution and two minutes of computing time.
Azure has two implementations of serverless compute:
- Azure Functions, which can execute code in almost any modern language.
- Azure Logic Apps, which are designed in a web-based designer and can execute logic triggered by Azure services without writing any code.
Data storage
Benefits
- Automated backup and recovery.
- Replication across the globe
- Data analytics.
- Encryption
- Data storage in virtual disks
- Storage tiers
- Multiple data types
- structured data aka databases
- semi-structured aka nosql
- unstructured data aka files
Services
- SQL Database is a relational database as a service (DaaS) based on the latest stable version of the Microsoft SQL Server database engine
- Cosmos DB is a globally distributed database service. It supports schema-less data that lets you build highly responsive and Always On applications to support constantly changing data.
- Blob Storage is unstructured,
- Data Lake allows you to perform analytics on your data usage and prepare reports. Data Lake is a large repository that stores both structured and unstructured data.
- Files offers fully managed file shares in the cloud that are accessible via the industry standard Server Message Block (SMB) protocol
- Queue storage is a service for storing large numbers of messages that can be accessed from anywhere in the world.
Storage tiers for blob object storage:
- Hot storage tier: optimized for storing data that is accessed frequently.
- Cool storage tier: optimized for data that are infrequently accessed and stored for at least 30 days.
- Archive storage tier: for data that are rarely accessed and stored for at least 180 days with flexible latency requirements.
Encryption for storage services
- Azure Storage Service Encryption (SSE) Azure encrypts the data before storing it and decrypts the data before retrieving it.
- Client-side encryption is where the data is already encrypted by the client libraries.
Networking
An N-tier architecture divides an application into two or more logical tiers. Architecturally, a higher tier can access services from a lower tier, but a lower tier should never access a higher tier.

A network security group, or NSG, allows or denies inbound network traffic to your Azure resources. Think of a network security group as a cloud-level firewall for your network.
Availability refers to how long your service is up and running without interruption.
High availability, or highly available, refers to a service that’s up and running for a long period of time.
Resiliency refers to a system’s ability to stay operational during abnormal conditions.
Azure Application Gateway. is a load balancer designed for web applications
Latency refers to the time it takes for data to travel over the network.
Bandwidth refers to the amount of data that can fit on the connection.
Traffic Manager uses the DNS server that’s closest to the user to direct user traffic to a globally distributed endpoint.
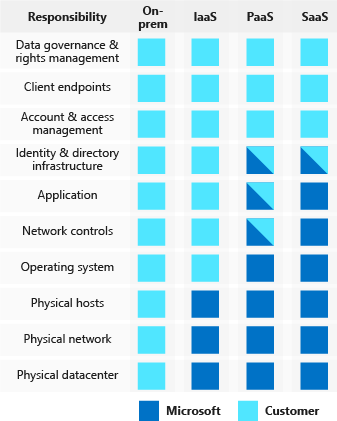
Security responsibilities
Defense in depth

Azure AD is a cloud-based identity service. It has built in support for synchronizing with your existing on-premises Active Directory or can be used stand-alone. Administrators and developers can control access to internal and external data and applications using centralized rules and policies configured in Azure AD.
A service principal is an identity that is used by a service or application. And like other identities, it can be assigned roles.
Azure AD Privileged Identity Management (PIM) is an additional, paid-for offering that provides oversight of role assignments, self-service, and just-in-time role activation and Azure AD and Azure resource access reviews.
Encryption
Azure Storage Service Encryption With this feature, the platform automatically encrypts your data before persisting it to Azure Managed Disks, Azure Blob storage, Azure Files, or Azure Queue storage, and decrypts the data before retrieval.
Azure Disk Encryption is a capability that helps you encrypt your Windows and Linux IaaS virtual machine disks.
Transparent data encryption (TDE) helps protect Azure SQL Database and Azure Data Warehouse performing real-time encryption and decryption of the database, associated backups, and transaction log files at rest.
KeyVault
Capabilities:
- Secrets management. You can use Key Vault to securely store and tightly control access to tokens, passwords, certificates, Application Programming Interface (API) keys, and other secrets.
- Key management. Key Vault makes it easier to create and control the encryption keys used to encrypt your data.
- Certificate management. Key Vault lets you provision, manage, and deploy your public and private certificates
- Store secrets backed by hardware security modules (HSMs). The secrets and keys can be protected either by software, or by FIPS 140-2 Level 2 validated HSMs.
Benefits
- Centralized application secrets.
- Securely stored secrets and keys.
- Monitor access and use.
- Simplified administration of application secrets. Key Vault makes it easier to enroll and renew certificates from public Certificate Authorities (CAs).
- Integrate with other Azure services.
Certificates
- Service certificates are used for cloud services
- Management certificates are used for authenticating with the management API
Network protection
- Azure Firewall is a managed, cloud-based, network security service that protects your Azure Virtual Network resources. It is a fully stateful firewall as a service with built-in high availability and unrestricted cloud scalability.
- Azure Application Gateway is a load balancer that includes a Web Application Firewall (WAF) that provides protection from common, known vulnerabilities in websites. It is designed to protect HTTP traffic.
- Network virtual appliances (NVAs) are ideal options for non-HTTP services or advanced configurations, and are similar to hardware firewall appliances.
ExpressRoute lets you extend your on-premises networks into the Microsoft cloud over a private connection facilitated by a connectivity provider.
Documents
Microsoft Azure Information Protection (sometimes referred to as AIP) is a cloud-based solution that helps organizations classify and optionally protect documents and emails by applying labels.
- Analyze data flows to gain insight into your business
- Detect risky behaviors and take corrective measures
- Track access to documents
- Prevent data leakage or misuse of confidential information
Advance threat protection
Azure Advanced Threat Protection (Azure ATP) is a cloud-based security solution that identifies, detects, and helps you investigate advanced threats, compromised identities, and malicious insider actions directed at your organization.
- Azure ATP portal
- Azure ATP sensors are installed directly on your domain controllers. The sensor monitors domain controller traffic without requiring a dedicated server or configuring port mirroring.
- Azure ATP cloud service runs on Azure infrastructure and is connected to Microsoft’s intelligent security graph.
Microsoft Security Development Lifecycle (SDL)
- Provide training
- Define security requirements
- Define metrics and compliance reporting
- Perform threat modeling
- Establish design requirements
- Define and use cryptography standards
- Manage security risks from using third-party components
- Use approved tools
- Perform Static Analysis Security Testing
- Perform Dynamic Analysis Security Testing
- Perform penetration testing
- Establish a standard incident response process
Policies
Azure Policy to create, assign and, manage policies. These policies enforce different rules and effects over your resources so that those resources stay compliant with your corporate standards and service level agreements.

An initiative definition is a set or group of policy definitions to help track your compliance state for a larger goal.
Azure Management Groups are containers for managing access, policies, and compliance across multiple Azure subscriptions.
Azure Blueprints enables cloud architects and central information technology groups to define a repeatable set of Azure resources that implements and adheres to an organization’s standards, patterns, and requirements.
Other policy def
The Microsoft privacy statement explains what personal data Microsoft processes, how Microsoft processes it, and for what purposes.
Trust Center is a website resource containing information and details about how Microsoft implements and supports security, privacy, compliance, and transparency in all Microsoft cloud products and services.
The Service Trust Portal (STP) hosts the Compliance Manager service, and is the Microsoft public site for publishing audit reports and other compliance-related information relevant to Microsoft’s cloud services.
Compliance Manager is a workflow-based risk assessment dashboard within the Service Trust Portal that enables you to track, assign, and verify your organization’s regulatory compliance activities
Azure Monitor maximizes the availability and performance of your applications by delivering a comprehensive solution for collecting, analyzing, and acting on telemetry from your cloud and on-premises environments.
Azure Service Health is a suite of experiences that provide personalized guidance and support when issues with Azure services affect you.
Resources
A resource group is a logical container for resources deployed on Azure.
- Consistent naming convention
- Organizing principles
- Organizing for authorization (RBAC)
- Organizing for life cycle
- Organizing for billing
Tags are name/value pairs of text data that you can apply to resources and resource groups.
Cost
The Azure pricing calculator is a free web-based tool that allows you to input Azure services and modify properties and options of the services.
Azure Advisor is a free service built into Azure that provides recommendations on high availability, security, performance, operational excellence, and cost.
Azure Cost Management is another free, built-in Azure tool that can be used to gain greater insights into where your cloud money is going.