Azure AD
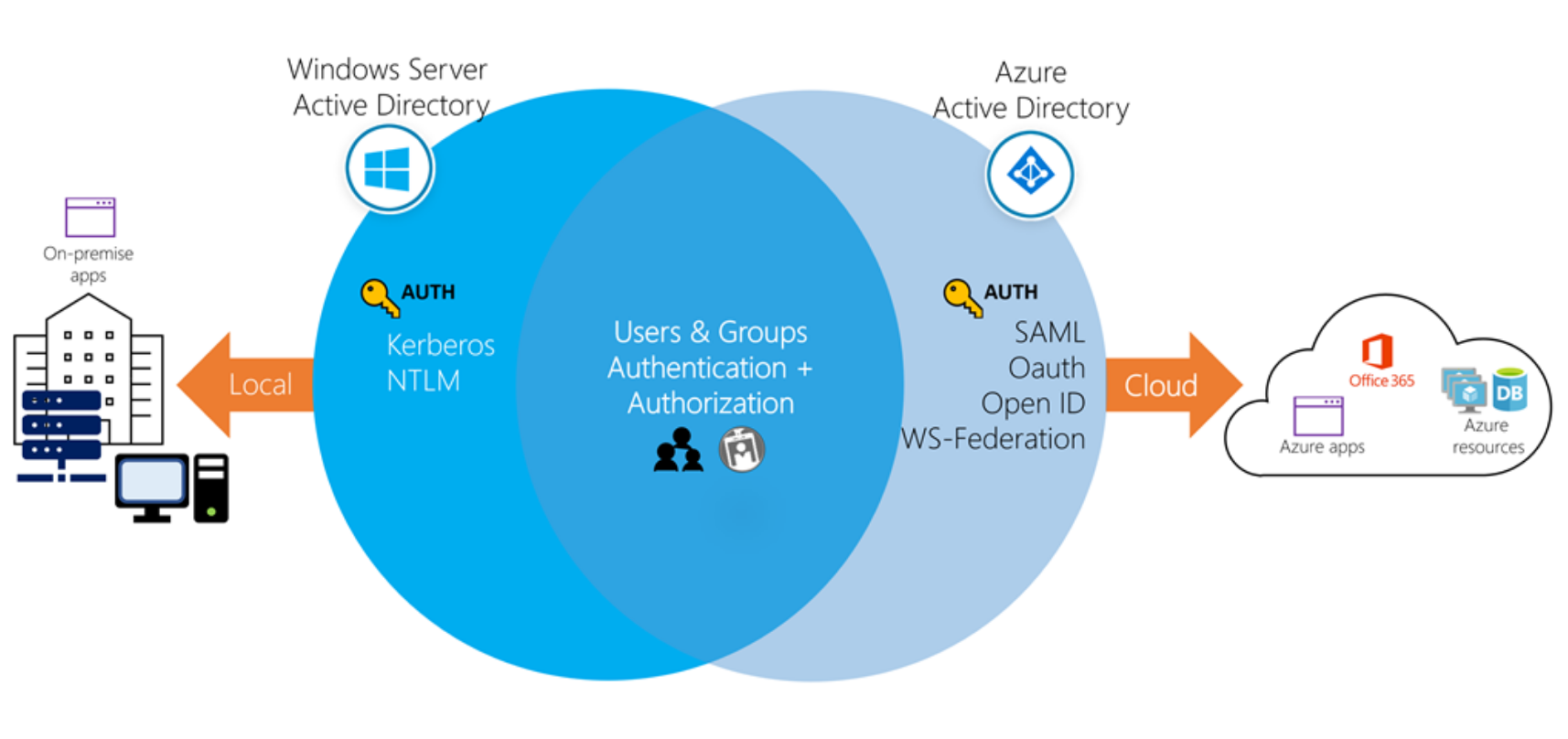
Azure AD is Microsoft’s cloud-based identity and access management service which provides single sign-on and multi-factor authentication. Azure AD is not a cloud version of Windows Server Active Directory. It’s also not intended as a complete replacement for an on-premises Active Directory. Instead, if you are already using a Windows AD server, you can connect it to Azure AD to extend your directory into Azure. This approach allows users to use the same credentials to access local and cloud-based resources.
Typically, Azure AD defines users in three ways:
Cloud identities – These users exist only in Azure AD. Examples are administrator accounts and users that you manage yourself.
Directory-synchronized identities – These users exist in an on-premises Active Directory. A synchronization activity that occurs via Azure AD Connect brings these users in to Azure. Their source is Windows Server AD.
Guest users – These users exist outside Azure. Examples are accounts from other cloud providers and Microsoft accounts such as an Xbox LIVE account.
OpenID
OAuth 2.0 is the industry-standard protocol for authorization.
OpenID Connect is an authentication layer that’s built on top of OAuth 2.0. It includes identity verification methods that are missing from OAuth 2.0. OpenID Connect gives you an access token plus an ID token, which you can send to an application to prove your identity.
A tenant is an instance of Azure AD that represents an organization. It’s a dedicated instance of Azure AD that an organization or app developer receives when the organization or app developer creates a relationship with Microsoft, like signing up for Azure, Microsoft Intune, or Office 365.